

In an era where cyber threats are becoming increasingly sophisticated, State, Local, Tribal, and Territorial (SLTT) government organizations face a daunting challenge in safeguarding critical data and public services with often limited budgets and staffing. These entities are prime targets for

In a startling revelation, the Federal Bureau of Investigation (FBI) has announced a $10 million reward for information leading to the identification or arrest of Russian Federal Security Service (FSB) cyber operators linked to a sophisticated campaign exploiting vulnerabilities in Cisco networking

As technology continues to reshape the fabric of society, few innovations have sparked as much intrigue and debate as cryptocurrency, a digital frontier that echoes the transformative journey of the internet decades ago. Both have emerged as game-changers, promising to redefine how value,

In an era where centralized cloud computing dominates the tech landscape, a bold contender has emerged to challenge the status quo with a revolutionary approach to harnessing computational power. Acurast, a decentralized compute network, has rolled out an innovative protocol update known as Staked
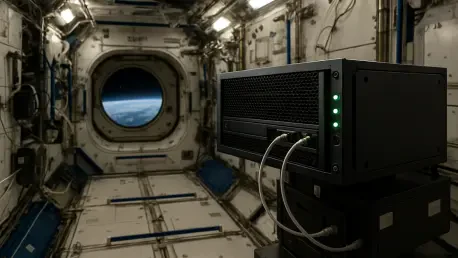
Picture a world where cutting-edge data processing happens not just on Earth, but 400 kilometers above, in the vacuum of space aboard the International Space Station (ISS). A pioneering project has pushed the boundaries of technology with the launch of the AxDCU-1, an orbital data center prototype,

In an era where digital footprints are constantly tracked, maintaining online privacy has become a pressing concern for millions of internet users, particularly those relying on Google Chrome, the world’s leading web browser. With its unparalleled speed and user-friendly interface, Chrome dominates

The Communication Services sector is capturing significant attention in the financial markets, demonstrating remarkable growth and positioning itself as a vital component of the modern economy with a year-to-date (YTD) return of 19.06%. This diverse industry encompasses a wide range of companies

In an era where digital transformation dictates the pace of business, cloud adoption has become an indispensable strategy for organizations striving to maintain a competitive edge, yet with the rapid integration of cloud technologies and AI-driven solutions, the shadow of cyber threats looms larger

The world of networking technology is undergoing a seismic shift, and at the heart of this transformation lies the critical role of network emulators, tools designed to replicate real-world network conditions for testing and optimization. A recently released comprehensive report, published on

I'm thrilled to sit down with Matilda Bailey, a renowned networking specialist with deep expertise in cellular, wireless, and next-gen solutions. With her finger on the pulse of the latest technologies and security trends, Matilda is the perfect person to help us unpack a critical issue in the
ITCurated uses cookies to personalize your experience on our website. By continuing to use this site, you agree to our Cookie Policy