
The persistent disconnect between technical network telemetry and the qualitative perception of a subscriber has remained one of the most significant hurdles for modern telecommunications operators. While a dashboard might show green across every key performance indicator, a user in a crowded

The increasing sophistication of contemporary cyber threats has forced a fundamental shift in how organizations conceptualize network security and threat mitigation strategies. As threat actors refine their methods, they frequently bypass traditional perimeter defenses by utilizing legitimate

The rapid expansion of low Earth orbit infrastructure has reached a critical turning point as the global demand for real-time data processing exceeds the capacity of traditional ground-linked systems. Open Cosmos has addressed this challenge by unveiling ConnectedCosmos, a sophisticated sovereign

Modern industrial facilities now face a paradoxical reality where the mechanical systems designed to last decades must defend against digital threats that evolve in milliseconds. The Industrial Cybersecurity Hardware Acceleration represents a significant advancement in the critical infrastructure

The sheer scale of global data processing has reached a point where the physical structures housing our digital lives must undergo a radical and immediate architectural metamorphosis to survive. As the digital economy expands at an unprecedented rate, the United States alone currently sees over

The Intersection of Digital Infrastructure and Synthetic Sociology The industrial landscape of the late twenty-twenties is being fundamentally reshaped by the paradox of needing massive digital growth while facing unprecedented local resistance to physical expansion. As the digital economy matures,

The traditional landscape of secure telecommunications is undergoing a fundamental shift as the Department of Defense releases the internal mechanics of its wireless networking software to the global community. By making the Open Centralized Unit Distributed Unit project available as open-source
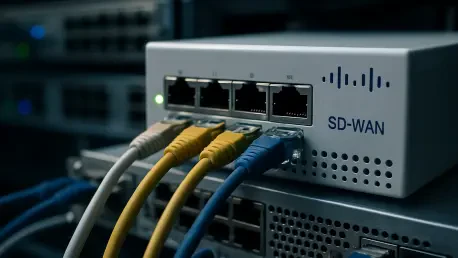
Modern enterprise connectivity relies on a delicate balance between accessibility and defense, yet recent discoveries regarding Cisco Catalyst SD-WAN systems reveal a sobering reality about how easily that balance can be shattered. Security researchers have confirmed that a critical vulnerability,

The global financial market witnessed a true statistical anomaly this week as the most prominent pioneer of artificial intelligence hardware posted financial results that exceeded the loftiest projections yet watched its market capitalization evaporate in days. Why did the world’s most valuable

The digital border between internal corporate networks and the chaotic public internet has become a theater of relentless, automated aggression where security sensors now log nearly 3 billion malicious sessions over a single six-month observation window. This translates to a staggering 212
ITCurated uses cookies to personalize your experience on our website. By continuing to use this site, you agree to our Cookie Policy