Modern enterprise networks have become so vast and fragmented that traditional perimeter defenses now resemble a picket fence attempting to stop a flood. As organizations grapple with the explosion of unmanaged devices and the blurring lines of the corporate perimeter, the concept of identity-driven network segmentation has emerged as a critical architectural shift. This technology moves beyond the antiquated reliance on IP addresses, which are increasingly transient and unreliable in a world of cloud instances and mobile workstations. Instead, it anchors security policies to the immutable characteristics of the devices and users themselves. This review examines how this transition from location-based to identity-based control is redefining the resilience of digital infrastructures.
The evolution of identity-centered security marks a departure from the “castle-and-moat” mentality that dominated the last two decades. Historically, segmentation required arduous manual configuration of Virtual Local Area Networks (VLANs) and Access Control Lists (ACLs), which often broke when a device moved to a different building or subnet. The current iteration of this technology utilizes a unified data layer to orchestrate security across the entire ecosystem. By integrating discovery, assessment, and governance into a single workflow, organizations can finally achieve a Zero Trust posture that remains consistent whether a user is in a corporate headquarters or a remote branch office.
The Evolution of Identity-Centered Network Security
The journey toward identity-driven security began with the realization that the network layer alone is insufficient for verifying trust. In the early stages, Network Access Control (NAC) provided basic “gatekeeper” functions, but it lacked the granularity to manage the lateral movement of threats once a device was inside. The emergence of sophisticated ransomware, which thrives by hopping across flat networks, necessitated a more dynamic approach. Today, identity-driven segmentation functions as a pervasive overlay, abstracting security logic from the underlying hardware to provide a more agile and responsive defense mechanism.
This technology is particularly relevant today because it addresses the “visibility gap” created by the Internet of Things (IoT) and Operational Technology (OT). Unlike standard laptops, these devices cannot host security agents, making them invisible to traditional endpoint detection tools. Identity-centered security fills this void by using passive and active monitoring to create a digital fingerprint for every asset. This shift ensures that security is no longer a static configuration but a continuous process of verification that adapts to the shifting technological landscape.
Core Architectural Components and Key Features
Advanced Zone Modeling and Device Identity
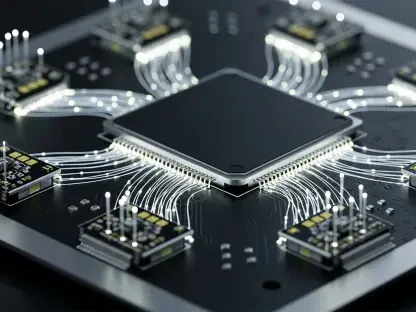
The heartbeat of modern segmentation lies in advanced zone modeling, a process that groups devices based on their function and risk profile rather than their network address. By analyzing over 1,200 unique attributes—ranging from hardware manufacturer to specific communication patterns—the system builds a persistent identity for every asset. This identity serves as the foundation for “zone constructs,” which are logical groupings that dictate who can talk to whom. If a device’s behavior changes or its risk level spikes, the system can automatically adjust its zone membership, ensuring that a compromised asset is isolated in real-time.
Furthermore, this identity-driven approach simplifies the management of complex environments. In a traditional setup, moving a server might require updating dozens of firewall rules across different segments. With identity-based modeling, the policy is tied to the server’s “fingerprint.” As the server moves, the policy follows it, significantly reducing the likelihood of human error during configuration. This performance gain is not just about security; it is about operational efficiency, allowing IT teams to focus on strategic initiatives rather than mundane ticket processing.
Agentless Discovery and OT Device Management
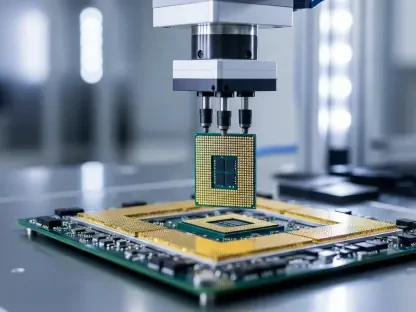
One of the most significant technical hurdles in network security is the presence of “unagentable” devices, such as medical imaging equipment or industrial controllers. These devices are often the weakest links in a network because they run on legacy operating systems that cannot be patched or monitored with standard software. Identity-driven platforms overcome this by employing agentless discovery methods, including header scraping and secure connect proxies. This allows the system to identify a device’s purpose and criticality without ever installing software on the endpoint itself.
The performance of these agentless methods is critical in heterogeneous environments where specialized hardware is the norm. For instance, in a smart manufacturing plant, the system must distinguish between a harmless sensor and a critical Programmable Logic Controller (PLC). By accurately identifying these assets, the platform prevents dangerous misclassifications that could lead to production downtime. This granular level of control ensures that sensitive OT environments are shielded from the broader corporate network, providing a vital layer of protection for essential services.
Current Trends in Multi-Vendor and AI Integration
The contemporary cybersecurity landscape is characterized by an increasing move toward vendor-agnostic solutions. Most large enterprises do not rely on a single hardware provider; they utilize a mix of switches, routers, and wireless controllers from various manufacturers. Identity-driven segmentation acts as a “translation layer” that works across this diverse hardware, enforcing a single, unified policy. This trend is a direct response to the operational silos that often plague IT departments, where different teams manage different brands of equipment using different security protocols.
Moreover, the integration of agentic AI is fundamentally changing how these platforms operate. New AI-driven dashboards can now correlate segmentation data with real-time threat intelligence to offer predictive insights. Instead of waiting for a breach to occur, the AI analyzes traffic patterns to identify “risky paths” that could be exploited. This transition from reactive to proactive security is a major shift in industry behavior, as organizations seek to automate the most complex aspects of threat hunting and risk mitigation.
Real-World Applications Across Heterogeneous Environments
In the healthcare sector, identity-driven segmentation is being used to protect life-critical devices from the vulnerabilities of the public internet. By creating isolated segments for MRI machines and infusion pumps, hospitals can ensure that even if a guest’s laptop is infected with malware, the virus cannot spread to the clinical network. This use case highlights the technology’s ability to manage high-stakes environments where downtime is not an option. The ability to model these segments against real-world traffic before enforcement ensures that no vital communication is blocked during the rollout.
Similarly, the financial services industry utilizes this technology to maintain compliance with strict data privacy regulations. By segmenting databases that contain sensitive customer information, banks can limit access to only the specific applications and users that require it. This “least-privilege” access model is a cornerstone of modern compliance frameworks. The flexibility of identity-driven systems allows these institutions to scale their security measures as they migrate workloads to the cloud, maintaining a consistent security posture across hybrid infrastructures.
Implementation Hurdles and Technical Constraints
Despite its advantages, the path to full segmentation is rarely smooth. One of the primary technical hurdles is the sheer volume of data generated by thousands of connected devices. Analyzing this data in real-time requires significant computational power and sophisticated algorithms to avoid false positives. If a security platform incorrectly identifies a critical server as a threat, it could trigger an automated quarantine that shuts down an entire business process. Consequently, the “test-before-enforce” phase is a non-negotiable step that many organizations find time-consuming.
Regulatory and cultural obstacles also play a role in slowing adoption. In many industries, there is a deep-seated fear that automation might lead to unintended outages. Overcoming this requires a shift in mindset, moving away from manual oversight toward trust in algorithmic decision-making. While ongoing development in AI and machine learning is helping to refine these systems and reduce errors, the initial investment in time and expertise remains a significant barrier for smaller enterprises with limited IT staff.
Future Outlook and the Path toward Autonomous Security
The trajectory of network security is pointing toward a future of fully autonomous, self-healing infrastructures. In this vision, identity-driven segmentation will not just be a tool for IT admins but a core component of a network that can sense and respond to threats without human intervention. Breakthroughs in edge computing will likely allow these security policies to be enforced closer to the device, reducing latency and further improving the speed of response. As these systems become more intelligent, the long-term impact will be a dramatic reduction in the “dwell time” of hackers within a network.
As we look forward, the convergence of identity, risk, and enforcement will lead to a more resilient society. The ability to isolate critical infrastructure—such as power grids or water treatment plants—at the first sign of a cyberattack could prevent large-scale catastrophes. This move toward autonomous security will eventually make the concept of a “flat network” a relic of the past, replacing it with a dynamic, multi-layered environment that is inherently resistant to intrusion.
Assessment of the Current Segmentation Landscape
The current state of identity-driven network segmentation revealed a significant leap in maturity for the cybersecurity industry. Organizations have moved beyond the experimental phase and are now deploying these systems at scale to solve the fundamental problems of visibility and control in complex environments. The transition from location-based logic to identity-centered intelligence has proven to be a decisive factor in stopping the lateral spread of modern threats. This approach successfully bridged the gap between legacy hardware and modern security requirements, providing a path forward for enterprises trapped in heterogeneous infrastructure cycles.
Actionable progress in this field now requires a focus on refining the integration between AI agents and human oversight. While the technology has matured, the next logical step for IT leadership is to invest in the data hygiene necessary to feed these identity-driven models. Future considerations must also include the standardization of identity protocols across different cloud providers to ensure that segmentation remains seamless in a multi-cloud world. Ultimately, the shift toward identity-driven control has established a new baseline for enterprise security, moving the industry closer to a reality where trust is never assumed and always verified.