Matilda Bailey is a distinguished networking specialist who has spent her career navigating the intricate intersection of hardware architecture and global security trends. With a focus on next-gen wireless and cellular solutions, she has become a leading voice for organizations looking to fortify their infrastructure against increasingly sophisticated state-sponsored threats. In this conversation, we explore the evolving landscape of network security, the impact of recent regulatory shifts regarding foreign-made equipment, and how the “bill of materials” has effectively become a geopolitical document for the modern enterprise.
The following discussion delves into the vulnerabilities of home-based hardware in a remote-work era, the strategic metrics for assessing state influence over networking equipment, and the delicate balance between hardware jurisdiction and technical resilience. We also address the practical challenges of domestic manufacturing and the risks of vendor lock-in as the pool of approved suppliers continues to narrow.
Consumer-grade routers are often the first line of defense for remote employees. How do these devices facilitate lateral movement into enterprise networks, and what specific protocols should security teams implement to verify the integrity of home-based hardware?
Consumer-grade routers are frequently the weakest link because they sit at the network edge while functionally serving as part of the enterprise control plane. When these devices are compromised, they act as a bridge, allowing malicious actors to tunnel into VPNs or exploit trusted connections to move laterally into sensitive corporate environments. To secure these unmanaged endpoints, security teams must first move beyond simple vulnerability patching and implement a Zero Trust Architecture that treats the home network as inherently hostile. This involves enforcing strict multi-factor authentication, using micro-segmentation to isolate remote traffic, and deploying endpoint detection and response (EDR) tools that monitor for anomalous behavior originating from the local gateway. Organizations should also provide a list of approved hardware or even ship enterprise-grade “remote kits” to employees to ensure that the hardware has verifiable firmware and no hidden backdoors.
Cyber campaigns like Volt Typhoon have utilized networking equipment to target vital infrastructure. What metrics should be used to assess the risk of state influence in a device, and how can a technical audit detect compromise when no public vulnerability has been disclosed?
Assessing state influence requires looking past traditional CVE scores and focusing on the jurisdiction of the manufacturer and the transparency of their software supply chain. We use metrics like the “Ownership and Jurisdiction Risk Score,” which evaluates the legal framework the vendor operates under, specifically regarding their obligation to cooperate with foreign intelligence services. In a technical audit where no public vulnerability is known, we look for “dark signals” such as unauthorized outbound connections to unusual IP ranges or undocumented administrative accounts hidden within the firmware. It is also vital to perform traffic analysis to detect data exfiltration patterns that may be masked as routine heartbeat signals or encrypted telemetry. By comparing the device’s behavior against a baseline of “known-good” operations, we can often spot the subtle footprint of a state-sponsored implant even without a formal bug disclosure.
Since networking hardware is increasingly viewed as a geopolitical document, how does shifting to allied-nation vendors change the risk profile for an organization? What are the trade-offs between hardware jurisdiction and the actual technical security of the equipment, and how can firms balance these competing priorities?
Shifting to allied-nation vendors significantly reduces the risk of state-mandated backdoors or supply chain interdiction by adversarial governments, effectively closing a major geopolitical exposure gap. However, it is a common misconception that changing the vendor’s geography eliminates technical risk; attackers have proven they can exploit vulnerabilities in “trusted” Western hardware just as effectively as in foreign-made gear. The trade-off is often one of “control versus compromise,” where you gain legal and political recourse but may still face the same baseline of software flaws. To balance these priorities, firms must conduct deep-dive technical due diligence regardless of the vendor’s headquarters. You should prioritize vendors that offer full transparency into their Hardware Bill of Materials (HBOM) and provide frequent, verifiable security updates to ensure that political trust is backed by technical rigor.
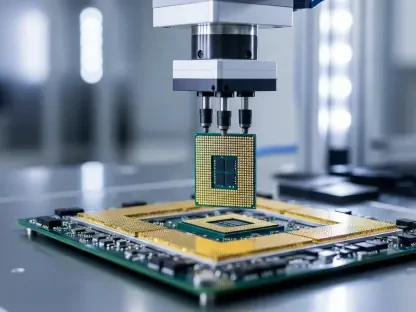
Domestic production of routers currently accounts for only a small fraction of the global market. Given the heavy reliance on international supply chains, what process should companies use to vet individual components, and how can hardware bill of materials transparency mitigate risks during the manufacturing phase?
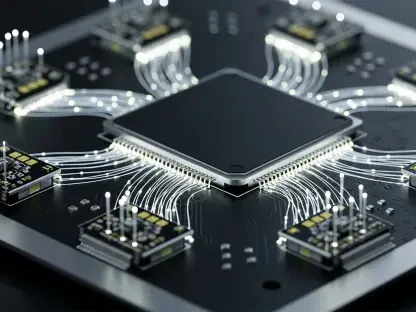
With domestic production in the US currently accounting for only about 10% of the market compared to the 60% to 75% produced in China and Taiwan, a purely domestic supply chain is currently a mathematical impossibility for most. To mitigate this, companies must adopt a rigorous “component-level” vetting process that tracks the origin of every integrated circuit and microchip. Hardware Bill of Materials (HBOM) transparency is the primary tool here, as it allows security teams to verify that no unauthorized third-party components were swapped in during the assembly phase. This transparency acts as a deterrent against “interdiction,” where hardware is intercepted and modified before it reaches the end user. By requiring manufacturers to provide a digital signature for the entire hardware stack, enterprises can programmatically verify the integrity of the device at the point of deployment.
A restricted list of approved suppliers can lead to vendor lock-in and reduced innovation. What strategies can enterprises use to maintain network resilience as the supplier pool shrinks, and how can a CISO prevent a single point of failure when working within a more restricted hardware ecosystem?
As the “covered list” of banned vendors grows, the shrinking pool of suppliers inevitably shifts pricing power to a few dominant players and can lead to a dangerous single point of failure. To counter this, CISOs should adopt an “Open Standards” strategy, ensuring that their network architecture is not dependent on proprietary features that tie them to one specific vendor’s ecosystem. By utilizing technologies like Software-Defined Networking (SDN), you can decouple the hardware layer from the control plane, making it easier to swap out physical devices without reconfiguring the entire environment. Additionally, enterprises should maintain a “multi-vendor allied strategy,” sourcing equipment from at least two different trusted jurisdictions to ensure that a security flaw or supply chain disruption in one region doesn’t take down their entire global infrastructure. This approach maintains a level of competition and keeps the pressure on vendors to continue innovating on security features.
What is your forecast for the future of network hardware security?
I anticipate that we are moving toward a “Verifiable Hardware” era where trust is no longer granted based on a vendor’s country of origin, but is instead mathematically proven through silicon-level roots of trust and real-time firmware attestation. We will likely see a significant rise in mandatory “Hardware Passports” that document every touchpoint in the manufacturing process, from the raw materials to the final shipping container. As geopolitical tensions continue to reshape the tech landscape, the ability to provide an auditable and transparent supply chain will become the single most important competitive advantage for networking companies. Ultimately, the industry will have to bridge the gap between the 10% domestic production and the overwhelming global demand by creating “Clean Rooms” of manufacturing that can exist even within high-risk jurisdictions under strict international oversight.