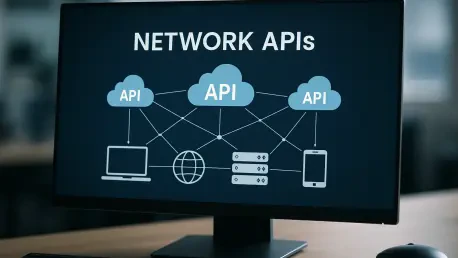
Digital identity verification is undergoing a seismic shift as traditional security measures like one-time passwords sent via text message are increasingly compromised by sophisticated cybercriminals using techniques like SIM swapping and social engineering. In response to these escalating threats, One New Zealand (One NZ) has formalized a strategic commercial agreement with Shush, a United States-based leader in carrier-grade network authentication, to deploy a sophisticated suite of Network Authentication APIs. This partnership marks a significant transition away from the friction-heavy and vulnerable methods of the past decade toward a model where security is integrated directly into the cellular infrastructure. By leveraging Shush’s advanced Sherlock platform, One NZ is transforming its mobile network into a proactive security asset that verifies identities in real-time without requiring any manual input from the customer. This move effectively replaces the outdated reliance on SMS-based codes with a more resilient and seamless silent authentication process. The integration of these APIs allows for the verification of a user’s identity by cross-referencing their mobile number with an active network session. This method ensures that the person attempting to access a service is indeed the legitimate owner of the device, providing an invisible yet iron-clad layer of protection. This strategic shift is not merely about technical upgrades; it represents a fundamental change in how telecommunications providers view their role in the broader digital economy, prioritizing trust and user experience above all else. By removing the need for users to wait for, copy, and paste verification codes, the system eliminates a major point of friction that often leads to abandoned transactions or user frustration. As businesses across New Zealand look for ways to enhance their digital presence, this initiative offers a clear path toward more secure and user-friendly interactions.
The Technical Foundation: Implementing the Sherlock Platform
At the core of this partnership is the implementation of the Sherlock platform, a comprehensive ecosystem featuring 47 network APIs that adhere to the highest global standards. These standards include the GSMA Open Gateway initiative, CAMARA, and TM Forum specifications, which ensure that the authentication services are interoperable and scalable across different markets and technology stacks. By adopting these unified standards, One NZ and Shush are providing developers with a consistent set of tools to build security features that work seamlessly across various mobile operating systems and device types. This standardization is crucial for widespread adoption, as it allows enterprises to integrate network-based authentication into their existing applications with minimal technical overhead. The Sherlock platform acts as a bridge between the complex internal systems of a mobile network operator and the external applications used by businesses, translating network signals into actionable security data. This allows for the immediate identification of potential fraud before it can impact the end user.
The specific technical capabilities of these APIs go far beyond simple identity checks, offering a granular level of verification that was previously unavailable to most commercial enterprises. For example, the system can detect if a SIM card has been recently swapped or if a mobile number is currently associated with a high-risk network session, triggering additional security protocols only when necessary. This selective approach preserves the user experience for the vast majority of legitimate customers while providing a robust defense against targeted attacks. Furthermore, the collaboration ensures that the authentication process is entirely silent, meaning it occurs in the background during the normal course of a user’s interaction with an app or website. This eliminates the wait-and-see period associated with SMS delivery, which is often subject to network congestion or international routing delays. By moving the authentication logic into the carrier network itself, One NZ is able to offer a level of certainty that third-party applications simply cannot match. This carrier-grade security provides a foundational layer of trust that is essential for high-stakes digital transactions.
Enhancing Security and Streamlining User Experience
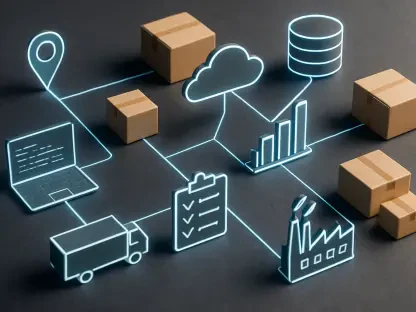
Beyond the technical architecture, this initiative addresses the critical need for a better balance between high-level security and consumer privacy. The network authentication system is engineered to confirm a user’s identity without the need to transmit or store excessive amounts of personally identifiable information. Instead of sharing detailed user profiles, the APIs provide a binary “yes” or “no” confirmation regarding the validity of a mobile session, which minimizes the data footprint of every transaction. This privacy-by-design approach is increasingly important as regulatory requirements around data protection become more stringent in New Zealand and abroad. Enterprises can now verify their customers with confidence, knowing they are not inadvertently creating new data silos or increasing their exposure to privacy-related risks. This methodology aligns with the modern expectations of consumers who demand both convenience and the assurance that their personal data is being handled responsibly. The result is a more secure digital ecosystem where the burden of proof is shifted from the user to the network.
For businesses, the transition to network-based APIs offers significant economic advantages that extend beyond the immediate prevention of fraud. Traditional SMS-based one-time passwords represent a recurring operational cost that can become substantial as a company scales its user base. By moving to a network API model, enterprises can reduce their reliance on these costly delivery channels while simultaneously decreasing the administrative overhead associated with managing forgotten passwords and account resets. This operational efficiency allows businesses to reinvest resources into core product development and customer engagement strategies. Moreover, the increased reliability of the onboarding process directly impacts conversion rates, as users are much more likely to complete a sign-up or purchase when the verification step is instantaneous. This commercial rollout, scheduled for the second quarter of 2026, positions One NZ as a strategic partner for any organization looking to optimize its digital journey. The move signals a broader trend where telecommunications providers act as the gatekeepers of digital trust, turning their network assets into valuable security services.
Strategic Future for Digital Identity Management
The successful deployment of these network-grade APIs necessitated a fundamental shift in how organizations conceptualized the relationship between connectivity and security. By integrating Shush’s Sherlock platform, One NZ established a precedent for the Asia-Pacific region, proving that mobile carriers could serve as the primary infrastructure for identity management. This transition allowed businesses to move away from fragmented security models toward a unified system that leveraged existing network signals for verification. The operational results demonstrated a marked decrease in account takeover attempts and a significant reduction in the costs associated with traditional SMS-based authentication methods. Enterprises that adopted these tools early on found that they could provide a much more streamlined onboarding experience, which directly translated into higher customer retention and satisfaction. This shift also empowered developers to create more innovative applications that did not require users to remember complex passwords or navigate multiple verification steps.
Looking ahead, the collaboration between telecommunications providers and network security specialists will likely focus on expanding these API capabilities to include more complex fraud detection signals and cross-border verification. Organizations should begin evaluating their current authentication workflows to identify where network-based verification can replace high-friction manual processes. The focus should be on integrating these APIs into the earliest stages of the user lifecycle, from initial sign-up to sensitive transaction authorization, to ensure a consistent security posture. As the digital landscape continues to evolve, the ability to provide invisible, instant, and iron-clad security will become a primary differentiator for businesses. Companies are encouraged to collaborate with their network providers to pilot these carrier-grade solutions, ensuring their systems are prepared for a future where the mobile network is the definitive source of identity. This proactive approach will be essential for maintaining a competitive edge in an environment where security and speed are equally prioritized.