The rapid proliferation of distributed workloads across multi-cloud and on-premises environments has created a level of operational complexity that traditional security management tools can no longer effectively address. To bridge this gap, Cisco has introduced the Mesh Policy Engine, a central component of its Security Cloud Control platform designed to unify disparate security architectures. This technology enables administrators to move away from managing individual device configurations and instead focus on high-level security intent that applies automatically across the entire network. By integrating hardware, virtual appliances, and cloud-native services into a single management plane, the engine addresses the friction inherent in modern enterprise infrastructures. Scheduled for a broad rollout next month, this advancement signals a shift toward more autonomous and intelligent network protection. The goal is to provide a seamless experience where security policies follow the data, regardless of where the underlying infrastructure resides or which vendor provides the specific firewall hardware. By leveraging automation to translate business requirements into technical rules, the platform reduces the burden on IT staff while simultaneously hardening the overall security posture against emerging threats.
Transitioning from Manual Rules to Intent-Based Security
Managing network access historically required a staggering amount of manual intervention, often involving cross-departmental coordination that could delay critical application deployments by several weeks. Security teams were forced to manually validate every access request against thousands of existing firewall rules to ensure that new permissions did not create unintended vulnerabilities or performance bottlenecks. This labor-intensive process was further complicated by the need to identify the exact path a packet would take through a labyrinth of physical and virtual firewalls, each requiring its own specific configuration syntax. Such a fragmented approach naturally increased the probability of human error, leading to security gaps that sophisticated attackers could exploit with ease. In the fast-paced digital environment of 2026, where business requirements change daily, relying on manual rule updates has become a significant liability that many organizations are no longer willing to tolerate because of the associated risks and the potential for costly downtime.
The Mesh Policy Engine addresses these systemic inefficiencies by introducing an intent-based management model that effectively separates business requirements from technical implementation details. Instead of meticulously writing individual rules for every firewall in a communication path, an administrator defines a broad security intent, such as authorizing a specific finance application to communicate with a database cluster over encrypted channels. The engine then performs a comprehensive analysis of the network topology, automatically identifying every enforcement point that sits between those two entities and generating the precise policies needed for each device. This automation ensures that security configurations are deployed in minutes rather than weeks, allowing the security posture to evolve in lockstep with application development cycles. By handling the underlying complexity of rule generation and deployment, the system allows security professionals to focus on strategic risk management rather than the minutiae of command-line interface updates or navigation through disparate management consoles.
Multivendor Compatibility and Infrastructure Optimization
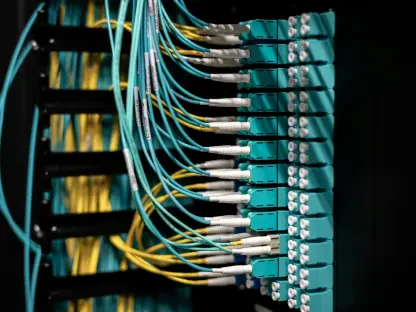
A major hurdle for many large enterprises is the heterogeneous nature of their security stack, which often includes a mix of legacy and modern equipment from multiple hardware vendors. Cisco has addressed this reality by ensuring that the Mesh Policy Engine supports multivendor interoperability, allowing it to manage third-party firewalls from prominent competitors like Palo Alto Networks, Fortinet, and Juniper. This pragmatic design choice prevents the need for a costly and disruptive “rip-and-replace” strategy, enabling organizations to leverage their existing investments while still benefiting from a centralized management plane. By providing a unified interface for diverse environments, the engine reduces the cognitive load on administrators who previously had to master multiple management consoles with varying logic and terminology. This level of integration is essential for maintaining a consistent security posture across a global enterprise that may have different vendors protecting different regional offices or data centers, ensuring that a single intent is enforced universally.
Beyond simple connectivity management, the engine provides powerful optimization tools designed to mitigate the risks associated with bloated and redundant firewall rule sets that accumulate over years of operation. Industry data suggests that a significant portion of firewall configurations consists of obsolete or redundant rules, which not only degrade device performance but also complicate the auditing processes required for regulatory compliance. The Mesh Policy Engine is capable of identifying and removing up to 80% of these redundant rules and approximately 35% of unnecessary objects, significantly streamlining the security configuration. This cleanup process is bolstered by advanced topology mapping, which gives administrators a transparent view of every traffic path and connection within the network. By visualizing the impact of a policy change before it is finalized, the system reduces the likelihood of unintended service disruptions. This level of clarity is vital for modern network segmentation, as it ensures that microsegmentation policies are applied accurately to prevent unauthorized lateral movement by threat actors.
Adapting to the Hybrid Mesh Firewall Architecture
The shift toward a hybrid mesh firewall architecture represents a direct response to the evolving nature of IT infrastructure, where data and workloads move fluidly between public clouds, private data centers, and edge locations. Industry analysts have increasingly recognized that the traditional perimeter-based security model is insufficient for protecting these highly distributed environments. Centralized management has emerged as a top priority for enterprise leaders who seek to reduce operational friction and gain consistent visibility across every layer of their network. Cisco’s strategic focus on the hybrid mesh model positions the company to provide a cohesive security framework that bridges the gap between cloud-native security groups and traditional on-premises appliances. This approach ensures that the same level of protection is applied to a containerized microservice in the cloud as it is to a legacy application running on a physical server. By unifying these disparate worlds, the engine helps organizations maintain compliance and security integrity in an era defined by constant change and architectural diversity.
This new engine works in concert with broader security innovations like Cisco Hypershield and Secure Workload to create a comprehensive defense-in-depth strategy for large-scale, automated environments. These tools allow for agent-based microsegmentation and distributed security enforcement, which are critical for protecting modern workloads against sophisticated internal and external threats. To simplify the financial and administrative aspects of this technology, Cisco has introduced a unified licensing model through its Cloud Protection Suite, allowing organizations to manage diverse deployment types under a single procurement umbrella. This flexibility is vital for businesses that are transitioning to the cloud at their own pace, as it allows them to reallocate security resources as their infrastructure needs evolve. By replacing fragmented security consoles with a centralized, intelligent system, the company is attempting to provide a platform that prioritizes operational reality over vendor lock-in, enabling organizations to achieve a more resilient and agile security posture that can adapt to the needs of the modern digital enterprise.
Future Proofing the Enterprise Security Posture
The launch of the Mesh Policy Engine provided a clear roadmap for organizations seeking to modernize their security operations by moving toward a more automated and intent-based framework. Security leaders who successfully integrated this technology focused on auditing their existing rule sets to take full advantage of the engine’s optimization capabilities, effectively reducing the attack surface by eliminating years of accumulated configuration debt. These organizations also prioritized training their staff to think in terms of business intent rather than device-specific commands, which accelerated the speed at which new digital services could be brought to market securely. The shift toward a hybrid mesh architecture allowed for a more consistent application of security policies across diverse environments, ensuring that protection remained robust even as workloads migrated between different cloud providers and local data centers. This transition proved essential for maintaining a competitive edge in an environment where speed and security are both paramount for business success.
Moving forward, the primary takeaway for IT administrators involved the necessity of embracing multivendor management platforms to avoid the complexities of maintaining siloed security environments. The ability to manage Cisco and third-party firewalls through a single interface demonstrated that interoperability is no longer just a convenience but a strategic requirement for global enterprises. Organizations were encouraged to adopt a phased approach to implementation, starting with the most critical traffic paths before expanding the engine’s reach across the entire network topology. By leveraging the comprehensive visibility provided by the platform, teams were able to identify and mitigate potential vulnerabilities before they could be exploited, transforming security from a reactive bottleneck into a proactive business enabler. Ultimately, the successful deployment of these automated tools required a fundamental shift in how security is perceived, moving away from static perimeters toward a dynamic, policy-driven model that can effectively protect the modern, distributed enterprise.