The shift from physical server rooms to distributed cloud environments has fundamentally rewritten the rules of engagement for digital defense, turning what was once a perimeter-based discipline into a complex war of identity management. As organizations migrate away from on-premises hardware, they trade the simplicity of a locked door for a sophisticated ecosystem where security is no longer a static shield but a dynamic, constant process of verification. This review explores the current state of these defenses, examining how they have evolved to meet the demands of a landscape where the “Shared Responsibility Model” dictates that while providers secure the underlying host, the clients themselves are entirely responsible for the integrity of their data and the behavior of their users.
The Foundations of Cloud Infrastructure Security
Cloud security has emerged as the cornerstone of modern IT, moving beyond traditional firewalls toward a decentralized model that prioritizes the protection of workloads wherever they reside. Unlike legacy systems that relied on a hard exterior to keep intruders out, modern cloud frameworks operate on the assumption that the network is already hostile. This necessitates a modular approach where every component—from virtual machines to serverless functions—must be independently secured and verified. This transition has forced a cultural shift in IT departments, requiring a deep understanding of how various cloud services interact and where the boundaries of liability lie between the organization and the service provider.
Relevance in today’s technological landscape is defined by the nuanced application of the Shared Responsibility Model. This framework is often misunderstood; many organizations mistakenly assume that by moving to the cloud, they are outsourcing their security risks. In reality, while a provider like Amazon Web Services or Microsoft Azure manages the physical security of data centers and the virtualization layer, the client retains full control—and full risk—over identity management, application security, and data encryption. This divide is where most modern failures occur, as the complexity of configuring these environments often outpaces the internal expertise of the institutions utilizing them.
Essential Components of Modern Cloud Defense
Identity and Access Management (IAM)
Identity and Access Management serves as the primary gatekeeping mechanism in the cloud, replacing the physical key with a complex web of digital credentials. Modern IAM functions through a combination of credential management and multi-factor authentication, with a growing emphasis on “Identity Center” sign-ons that centralize control. By using short-lived credentials instead of static keys, organizations can significantly reduce the window of opportunity for an attacker. The objective is to ensure that even if a password is stolen, the lack of a secondary physical token or the expiration of the session token renders the stolen information useless within minutes.
Environment Segmentation and Isolation
Beyond mere access control, the technical isolation of environments is a critical deterrent against sophisticated threat actors. By separating development, testing, and production environments into distinct tenants or “Organizations,” security teams can prevent lateral movement—a tactic where an attacker gains entry through a low-security portal and migrates toward high-value data. This architectural “air-gapping” ensures that a breach in a public-facing web server does not automatically grant access to the core database. This level of segmentation requires rigorous discipline, as it often complicates the workflow for developers, yet it remains the most effective way to contain a compromise.
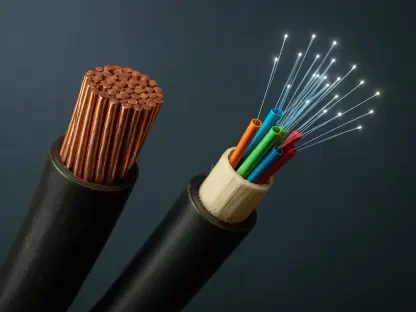
Data Encryption and Integrity Monitoring
The performance characteristics of encryption have improved to the point where at-rest and in-transit protection are now industry standards with negligible latency. However, encryption alone is not a panacea; it must be paired with continuous integrity monitoring to detect large-scale data exfiltration in real time. Advanced monitoring tools now use behavioral analytics to identify anomalies, such as an administrative account accessing thousands of files at an unusual hour. These systems provide the necessary visibility to catch a breach while it is in progress, rather than discovering the loss months later when the data appears on a leak site.
Emergent Trends and Shifts in the Threat Landscape
The threat landscape has undergone a significant transformation, moving away from simple financial extortion toward “leak-and-shame” hacktivism. This shift is particularly visible in attacks targeting public institutions, where the goal is not to encrypt data for a ransom but to broadcast sensitive information to inflict reputational and political damage. This pivot suggests that traditional backup strategies, which protect against ransomware, are insufficient against actors who simply want to embarrass their targets. Consequently, the focus is shifting toward preventing any form of unauthorized data egress, regardless of whether the system remains operational.
In response to the increasing frequency of credential harvesting, industry behavior is gravitating toward a “zero-trust” architecture. This philosophy dictates that no user or device is trusted by default, even if they are already inside the corporate network. Every request for access must be continuously authenticated and authorized based on a variety of contextual signals, such as geographic location and device health. This move away from “implicit trust” is a direct reaction to the reality that human error—specifically falling for sophisticated phishing schemes—is the most consistent vulnerability in even the most technically advanced cloud setups.
Real-World Applications and Institutional Implementations
Public sector bodies and international governing agencies, such as the European Commission, represent the most high-stakes use cases for cloud security. For a platform like Europa.eu, the challenge is to maintain a balance between public accessibility and the protection of sensitive stakeholder data. These institutions often manage hundreds of gigabytes of information that, while not classified, is politically sensitive. The unique difficulty for these organizations lies in their scale; they must secure a massive, diverse user base while defending against state-sponsored actors who have the resources to wait for a single administrative mistake.
The implementation of cloud security in these environments often reveals a friction between transparency and safety. Large-scale web platforms are designed to be reached by everyone, yet the administrative backend must be invisible. When these entities fail, it is rarely due to a failure in the cloud provider’s hardware; rather, it is usually a breakdown in the governance of the cloud environment itself. The institutional challenge is therefore as much about policy and training as it is about technical configuration, as the sheer volume of data makes traditional manual oversight impossible.
Persistent Challenges and Operational Hurdles
A significant gap persists between regulatory compliance and real-world operational security. Organizations may meet all the requirements of frameworks like the EU’s cybersecurity regulations, yet remain vulnerable to basic attacks. Compliance often focuses on documentation and periodic audits, whereas security requires constant, proactive vigilance. This “compliance trap” can lead to a false sense of security, where teams check off boxes on a list while failing to address the underlying risks of static IAM keys or poorly configured permissions that exist in the “gray areas” of the cloud.
The “human factor” remains the most persistent hurdle, transcending even the most robust cloud architectures. Whether it is a developer accidentally hardcoding an API key into a public repository or an administrator bypassing multi-factor authentication for convenience, the majority of breaches originate from a human choice. Managing this risk requires more than just better software; it requires operational protocols like “break glass” systems, where administrative access is only granted through dual-authorization. These technical hurdles are necessary friction points that prevent a single compromised account from cascading into a full-scale catastrophe.
Future Outlook and the Era of Digital Sovereignty
The future of cloud security is increasingly tied to the concept of digital sovereignty, with a clear move toward localized or “EU-made” cloud solutions. This trend stems from a desire to reduce dependence on foreign-owned infrastructure providers and to ensure that data is governed by regional laws and security standards. While transitioning to local providers does not inherently solve identity management issues, it allows for more direct oversight of the physical and legal layers of the stack. This shift is likely to redefine the market, creating specialized “sovereign clouds” for government and high-security industrial sectors.
Looking ahead, the rise of “cyber-mercenary” activity will likely drive the adoption of even more restrictive administrative protocols. We can expect a wider implementation of hardware-based tokens and biometric verification as the standard for all cloud interactions. Furthermore, the long-term impact of dual-authorization protocols will change the nature of IT administration, making it a collaborative rather than an individual task. These developments indicate that the future of cloud defense will be characterized by a “constant fear” mindset, where security is treated as a core business function rather than an IT afterthought.
Summary and Overall Assessment
The review of cloud infrastructure security highlighted that while the technical tools for defense are more advanced than ever, the human element remains a volatile variable. The analysis showed that the most damaging breaches often result from the failure to manage basic digital identities rather than flaws in the cloud providers themselves. It was clear that the “Shared Responsibility Model” is a double-edged sword; it offers flexibility but places a massive burden of configuration on the client. The shift toward “zero-trust” and digital sovereignty marked a realization that institutional integrity can no longer rely on simple compliance.
The investigation into recent high-profile compromises revealed that the motive for cyberattacks is moving beyond financial gain toward geopolitical disruption. This evolution necessitated a shift in defensive strategy, focusing on containment and the elimination of static credentials. Ultimately, the state of cloud security was found to be a race between increasingly sophisticated automation and the persistent reality of human error. Moving forward, the most successful organizations were those that prioritized identity-centric protection and adopted a proactive posture, treating every access request as a potential threat in an era where the digital perimeter has effectively vanished.