The modern enterprise environment has reached a point where a single misplaced semicolon in a third-party routing table can cause more financial damage than a physical data center fire. As organizations have matured in their cloud-native journeys, a sophisticated discipline has emerged around protecting core databases and virtualized servers. However, this progress has inadvertently created a massive technical debt regarding the network control plane. While the interior of the cloud is often a masterpiece of automation, the exterior—the pathways managed by entities like Cloudflare, Akamai, and F5—frequently remains a fragile collection of manual entries and unversioned scripts. This analysis examines the strategic expansion of ControlMonkey’s Disaster Recovery platform, which now brings these critical third-party network services into a unified, automated recovery framework.
Bridging the Configuration Gap in Modern Cloud Infrastructure
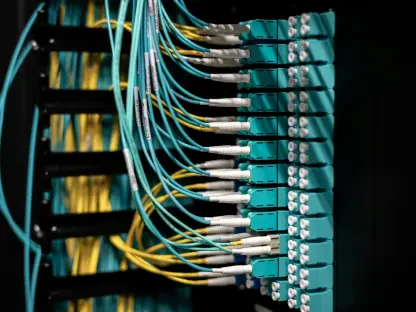
The rapid shift toward decentralized cloud architectures has fundamentally altered how global enterprises scale and manage their digital presence. While organizations are now adept at protecting primary data, a critical vulnerability has emerged within the network control plane. Often, the configurations governing traffic remain isolated from standard automated recovery protocols. This isolation means that even if a company possesses a perfect backup of its application data, it may remain effectively offline if the external network settings that direct users to that data are compromised or deleted.
ControlMonkey is addressing this “blind spot” by expanding its platform to include comprehensive support for third-party network services. By shifting from a purely data-centric recovery model to one that prioritizes the network control plane, the company aims to ensure that organizations remain reachable and resilient. The focus is no longer just on whether the server is running, but whether the global internet knows how to find it. This transition reflects a broader market need to treat external dependencies with the same level of scrutiny as internal infrastructure.
The Evolution of Resiliency: From Data Backups to Control Plane Integrity
Historically, disaster recovery was synonymous with data redundancy. If a primary server failed, a business would simply switch to a backup database in a different geographic region. However, as infrastructure has become more fragmented across various edge providers and content delivery networks, the definition of recovery has been forced to evolve. Modern downtime is frequently caused not by the loss of the data itself, but by the loss of the “map” that directs users to that data.
Past developments in the industry focused heavily on Infrastructure-as-Code for primary cloud providers. While this revolutionized the management of virtual machines, third-party network services were often left behind, managed through manual dashboards or legacy scripts. This historical separation created a dangerous gap: an organization could have a perfectly redundant database but still suffer total downtime if its web application firewall or DNS settings were misconfigured. There was no automated way to restore these external settings, leading to prolonged outages during high-stress recovery scenarios.
Automating the Invisible: Bringing DevOps Rigor to Third-Party Networks
Addressing the Infrastructure-as-Code Coverage Gap
A significant challenge in modern IT operations is the lack of version control for third-party network configurations. A vast majority of enterprises do not use Terraform or similar tools to manage services like Cloudflare or Akamai, relying instead on manual adjustments through web consoles. ControlMonkey addresses this by using proprietary technology to reverse-engineer live network states into Terraform code. This process effectively transforms “dark” infrastructure into versioned code, allowing teams to audit, track, and restore network settings with the same precision applied to their primary cloud servers.
The Lifecycle: Network Configuration Recovery
The platform introduces a structured workflow designed to eliminate manual errors and ensure continuous protection. This begins with a comprehensive asset inventory that identifies every active resource across the network stack. By identifying gaps—resources not currently managed by code—the system provides IT leaders with a clear roadmap of their unprotected surface area. Once mapped, the platform takes daily snapshots of the environment, creating a historical record that serves as a reliable “undo” button for the entire network infrastructure.
Mitigation: Configuration-Level Disasters and AI Errors
While provider-side outages are rare, configuration-level disasters are an escalating threat. This technology is specifically designed to combat risks such as ransomware attacks that target the network control plane to “black out” an organization. Additionally, as enterprises deploy AI agents for automated infrastructure management, the risk of high-speed, large-scale misconfigurations grows. By providing a one-click restore capability, the platform ensures that whether a failure is caused by a malicious actor or a buggy AI script, the organization can return to a known-good state in minutes.
Future Trends in Cyber Resilience and Compliance
The expansion of disaster recovery into the network layer signals a broader shift toward “Configuration-as-Code” across all third-party dependencies. As regulatory frameworks place greater emphasis on business continuity, the ability to prove that network configurations are backed up and restorable will become a standard compliance requirement. We have entered an era where cyber resilience is viewed as a three-legged stool consisting of data protection, infrastructure automation, and network control plane recovery.
Looking ahead, we can expect to see deeper integrations between recovery platforms and observability tools. AI-driven monitoring systems will likely detect unauthorized or erroneous configuration changes and automatically trigger restorations before the change even impacts end-users. This proactive, self-healing infrastructure is rapidly becoming the benchmark for enterprise stability, moving beyond reactive patching toward an era of perpetual uptime through automated vigilance and rapid state restoration.
Actionable Strategies for Enhanced Business Continuity
To capitalize on these advancements, organizations should conduct a configuration audit to identify which parts of their network stack are currently managed manually. Transitioning these services to a code-based recovery model should be prioritized to eliminate single points of failure. Furthermore, businesses should integrate their disaster recovery snapshots with automated playbooks, ensuring that the recovery process is not dependent on manual intervention during a high-stress outage.
Best practices now dictate that network configurations should be treated with the same level of security and versioning as application source code. By adopting a configuration-centric recovery strategy, IT leaders can move beyond reactive troubleshooting. Establishing a robust, automated defense against the most common causes of modern downtime requires a commitment to visibility and the elimination of manual “shadow” configurations that exist outside the standard DevOps pipeline.
Securing the Future of Connectivity
ControlMonkey’s expansion into third-party network configuration recovery addressed a persistent and dangerous gap in cloud management. By enabling the backup and restoration of the network control plane, the platform ensured that the pathways connecting users to services were as resilient as the data itself. The move signaled a fundamental requirement for any enterprise committed to long-term operational stability. The ability to treat every aspect of the network as restorable code proved to be the missing link in the quest for total digital sovereignty and resilience against the complexities of a fragmented cloud landscape.