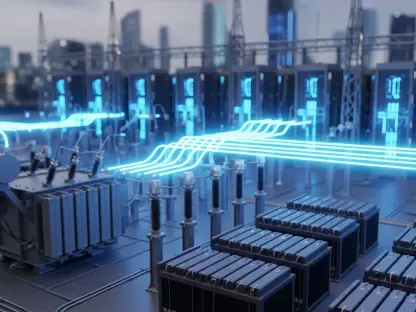
Modern industrial facilities now face a paradoxical reality where the mechanical systems designed to last decades must defend against digital threats that evolve in milliseconds. The Industrial Cybersecurity Hardware Acceleration represents a significant advancement in the critical infrastructure and manufacturing sectors. This review explores the evolution of the technology, its key features, performance metrics, and the impact it has had on various applications. The purpose of this review is to provide a thorough understanding of the technology, its current capabilities, and its potential future development.
The Evolution of Hardware-Accelerated Industrial Defense
Traditional cybersecurity models relied almost exclusively on software layers that operated on top of standard operating systems. In the context of industrial control systems, this approach often proved disastrous because the central processing units in these environments were never designed to handle the heavy computational overhead of modern encryption and traffic monitoring. As the threat landscape expanded, the limitations of software-only models became apparent, leading to a fundamental shift toward hardware-centric defense mechanisms.
This evolution was driven by the necessity to protect operational technology without sacrificing the deterministic performance required for physical processes. By embedding security protocols directly into the silicon, engineers created a foundation where protection is no longer an external addition but a native property of the network. This technological shift reflects a broader trend in the industry where hardware isolation is prioritized to ensure that a compromise at the software level does not grant an adversary control over critical physical assets.
Core Architectural Components of Hardware Acceleration
Data Processing Units (DPUs) and Computational Offloading
At the heart of this hardware revolution lies the Data Processing Unit, a specialized class of programmable processor designed to handle data-centric workloads. Engines like the Nvidia BlueField function as the primary defense coordinators, effectively offloading intensive security tasks from the host processor. This offloading is vital because it preserves the computational resources of the industrial machine, allowing the main CPU to focus entirely on its primary automation tasks without being bogged down by the telemetry demands of modern security platforms.
What distinguishes this architecture from traditional network interface cards is its ability to operate as a “computer in front of the computer.” The DPU provides a physically isolated execution environment for security services, meaning that even if the primary server or industrial controller is compromised, the security policies enforced by the hardware remain intact. This level of isolation creates a robust barrier that competitors relying on software-based virtualization simply cannot match, offering a more reliable foundation for high-stakes industrial environments.
Deep Packet Inspection and Identity-Based Access
The integration of hardware acceleration allows for deep packet inspection to occur at wire speed, a feat previously impossible in high-throughput industrial networks. In aging operational technology environments, where “fragile” systems often crash when subjected to heavy scanning, hardware acceleration provides a non-intrusive way to monitor traffic. By analyzing every packet in transit at the silicon level, the system can identify malicious patterns and unauthorized commands without introducing the latency that would disrupt sensitive manufacturing processes.
Moreover, this technology enables micro-segmentation based on the specific identities of devices and users. Instead of relying on broad network rules, hardware-accelerated systems enforce granular, identity-based access controls that ensure only authorized entities can interact with specific components. This capability transforms the network into a series of isolated “secure zones,” preventing the lateral movement of threats. This approach is particularly effective in legacy environments where updating the internal security of the machines themselves is not a viable option.
Emerging Trends in Distributed Intelligence
The current trajectory of industrial defense is moving rapidly toward decentralized architectures that leverage “agentic AI” for autonomous threat mitigation. Rather than sending massive amounts of raw data to a central cloud for analysis, modern hardware-accelerated systems process intelligence at the edge. This shift reduces the time required to detect an intrusion from minutes to microseconds, allowing the network to self-correct and isolate compromised segments before physical damage can occur.
This trend is also marked by a significant departure from the traditional “air gap” model, which assumed that physical isolation was enough to protect industrial assets. As industries embrace interconnected, AI-driven ecosystems, the focus has shifted to building resilience within a permanently connected state. The industry behavior now favors systems that can maintain security integrity through constant, hardware-enforced monitoring, acknowledging that the perimeter has effectively vanished in the modern era of industrial automation.
Real-World Applications and Sector Deployment
Secure Edge Infrastructure in Manufacturing
In the manufacturing sector, the deployment of AI-ready industrial data centers has revolutionized how data flows between the factory floor and the cloud. Leading platforms, such as those developed by Siemens, utilize hardware acceleration to create a secure edge that acts as a gatekeeper for industrial workloads. This setup ensures that high-speed data acquisition for predictive maintenance or quality control does not become a vector for cyberattacks, providing a safe conduit for information exchange.
These implementations demonstrate the practicality of hardware acceleration in high-volume production environments. By offloading security protocols to specialized hardware, manufacturers maintain the throughput necessary for competitive operations while adhering to strict security standards. The result is a more resilient supply chain where the risk of production downtime due to a digital breach is significantly mitigated through localized, high-performance defense mechanisms.
Zero-Trust Architectures in Critical Infrastructure
Critical infrastructure, particularly the energy sector, has seen a unique application of identity-based controls enforced at the hardware level. In these high-consequence environments, zero-trust architectures ensure that every request for access is verified, regardless of its origin. Hardware acceleration allows these systems to manage complex “least-privilege” access policies in real-time, protecting vital assets like power grids and water treatment plants from unauthorized manipulation.
By enforcing these policies at the hardware level, operators can manage third-party access and remote maintenance with a high degree of confidence. The hardware serves as an immutable point of truth, ensuring that human errors or software vulnerabilities do not lead to catastrophic physical outcomes. This deployment model has become a standard for organizations looking to meet rigorous regulatory requirements while modernizing their aging infrastructure for a more connected future.
Implementation Challenges and Technical Hurdles
Despite the clear advantages, the integration of modern DPUs with legacy “fragile” systems presents significant technical hurdles. Many industrial machines were designed before the internet existed, and their communication protocols often lack the standardization required for seamless integration with high-speed security hardware. Navigating this complexity requires sophisticated engineering to ensure that the introduction of modern security measures does not inadvertently cause the very downtime they are meant to prevent.
Furthermore, the regulatory landscape governing critical infrastructure adds another layer of difficulty to implementation. Compliance with varying global standards can slow the adoption of new technologies as organizations struggle to prove that hardware changes meet safety and reliability mandates. Ongoing development efforts are focused on agentless security models, which require no software changes to the existing machines, thereby bypassing the need for risky updates to the core logic of legacy industrial controllers.
Future Outlook and Technological Trajectory
The technological trajectory of hardware acceleration points toward the development of fully autonomous, self-healing industrial networks. In these future systems, the hardware will not only detect and block threats but will also automatically reconfigure the network to maintain operational continuity during an attack. This capability would represent the pinnacle of industrial resilience, where the system itself acts as an intelligent, defensive organism capable of surviving sophisticated cyber-physical warfare.
The long-term impact of “secure-by-design” infrastructure will likely extend to global supply chain resilience and the overall safety of physical operations. As hardware-accelerated security becomes a standard component of industrial hardware, the cost of protection will decrease while its effectiveness increases. This shift will fundamentally change the economics of cybercrime, making industrial targets much more difficult and less profitable to attack, ultimately fostering a safer and more stable global industrial landscape.
Summary and Overall Assessment
The shift from software-based security layers to embedded hardware acceleration represented a decisive turning point in the protection of global industrial assets. By moving the burden of security from the host CPU to specialized DPUs, the industry achieved a level of isolation and performance that was previously unattainable. This transition allowed for the enforcement of zero-trust principles and real-time packet inspection within even the most sensitive and aging operational technology environments, effectively closing the gap between modern threats and legacy defenses.
The assessment of the technology’s current state revealed a robust and rapidly maturing field that has become essential for the survival of interconnected critical infrastructure. While integration challenges with legacy systems remained a notable hurdle, the rise of agentless, hardware-enforced models provided a clear path forward. The movement toward decentralized, AI-driven intelligence suggested that the next generation of industrial networks would be defined by their ability to self-defend. Ultimately, hardware acceleration proved to be the fundamental role in safeguarding the physical world, ensuring that the progress of automation did not come at the cost of security.