The fundamental concept of how nations and large-scale enterprises manage their most sensitive information is undergoing a profound structural realignment that favors physical possession over remote accessibility. For years, the prevailing wisdom suggested that digital sovereignty could be achieved simply through data residency, where information remained within a specific geographic border while being managed by global cloud hyperscalers. However, as geopolitical tensions rise and the technical complexities of modern infrastructure evolve, this hands-off approach has proven insufficient for entities requiring absolute control over their operational destiny. We are witnessing a decisive shift from “contractual sovereignty”—where organizations rely on the promises of service providers—to “full-stack” on-premises sovereignty, where the network, compute power, and management control planes are physically and logically isolated within the owner’s own facilities. This move is not merely a reaction to security threats but a strategic effort to ensure that the “kill switch” for critical services remains in local hands, immune to foreign legal reach or the unilateral decisions of international technology vendors.
This transition has been catalyzed by a series of high-profile strategic pivots in Europe, where government bodies are actively decoupling their core communications from American-led cloud ecosystems. France, for instance, has aggressively moved toward replacing ubiquitous collaboration platforms like Microsoft Teams and Zoom with Visio, a domestically produced alternative that offers greater transparency and jurisdictional alignment. Similarly, the Austrian Ministry of Economy, Energy, and Tourism made headlines by rejecting standard cloud-based productivity suites in favor of an open-source architecture hosted entirely on its own internal servers. These decisions signal a broader consensus among policymakers that true data autonomy cannot exist if the underlying software execution environment is governed by entities subject to foreign surveillance laws. By moving back to on-premises infrastructure, these organizations are reclaiming the ability to audit every line of code and every hardware configuration, ensuring that their digital foundations are as secure and sovereign as their physical borders.
Geopolitical Risks and the Reality of Control Planes
A primary driver for the current migration toward on-premises solutions is the increasing awareness of how legal compulsion functions in a globalized digital economy, specifically regarding the reach of U.S. data access laws. Even when a global cloud provider stores data on servers located physically within a European or Asian country, those providers remain legal entities subject to the mandates of their home jurisdictions, which may require them to grant access to sensitive information without the knowledge of the data owner. This inherent conflict of interest has led many highly regulated enterprises to conclude that residency is a hollow protection if the provider maintains the administrative keys. By repatriating these workloads to local, on-premises environments, organizations effectively eliminate the possibility of a third party being forced to bypass their security protocols. This architectural independence ensures that the organization remains the sole arbiter of who accesses its data, providing a level of legal and operational certainty that cloud-based residency models simply cannot replicate in the current global climate.
Furthermore, the distinction between where data “sits” and who “governs” it has become a central point of contention for modern IT departments. While hyperscalers have become adept at meeting residency requirements, they typically retain absolute ownership of the control plane—the management layer that orchestrates how data is processed, moved, and secured. If an organization does not own the control plane, it does not truly own its digital infrastructure; it merely rents a slice of someone else’s logic. On-premises sovereign solutions return this governance layer to the enterprise, allowing it to define and enforce its own security policies without interference from an external provider’s global updates or configuration changes. This shift represents a move toward deep-seated operational autonomy, where the ability to direct the flow of information is treated as a core component of national or corporate security rather than a convenient service to be outsourced. Consequently, the move to on-premises is less about the physical location of servers and more about the reclamation of the decision-making logic that sits at the heart of the modern digital enterprise.
The AI Sovereignty Imperative and Local Inference
The rapid integration of Large Language Models and generative AI into the enterprise stack has introduced a new and volatile variable into the sovereignty equation. When an organization interacts with a cloud-based AI service, it often feeds highly proprietary prompts, customer data, and intellectual property into a black-box environment where data lineage and future use are difficult to track. There is a growing concern that this telemetry and metadata could be used to train future models or inadvertently leak sensitive trade secrets to competitors who use the same global service. To counter this, the move toward on-premises digital sovereignty now prioritizes local AI inference, where models are deployed on internal CPU and GPU clusters. This allows organizations to harness the transformative power of AI while ensuring that every interaction remains within a strictly defined sovereign boundary, never leaving the private network to touch a third-party server. This level of containment is becoming the gold standard for organizations that view their data as a primary competitive advantage.
This localized approach to artificial intelligence also addresses the critical need for transparency in model behavior and decision-making processes. In a sovereign on-premises environment, developers and security auditors can implement rigorous testing and monitoring of AI models without the constraints or obfuscation often found in public cloud APIs. This transparency is essential for meeting emerging regulatory requirements that demand explainability in automated decision-making, particularly in sectors like finance, healthcare, and public administration. By hosting AI workloads locally, organizations can ensure that the weights, biases, and training data of their models are protected from external tampering or unauthorized observation. This paradigm shift ensures that as AI becomes more central to operational efficiency, the control over those systems remains an inherent property of the organization’s own infrastructure, preventing a new form of “AI colonialism” where intelligence and data are concentrated in the hands of a few global providers.
Vendor Strategies for Sovereign Infrastructure
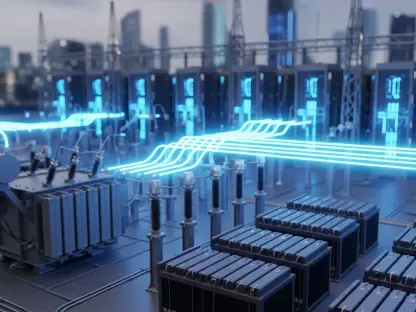
In response to the growing demand for autonomy, major technology providers are reinventing their offerings to support “air-gapped” and physically isolated environments. Cisco has taken a leadership role in this space by introducing its Sovereign Critical Infrastructure portfolio, which includes specialized licensing models for routing, switching, and wireless hardware that do not require a persistent connection to a central cloud for management or validation. This is a significant departure from the industry trend of “as-a-service” management, as it places the entirety of the operational power back in the customer’s hands. Cisco’s approach is specifically designed for environments where even a momentary leak of telemetry data could be catastrophic. By explicitly relinquishing the ability to remotely disable or manage these products, the vendor provides a technical guarantee that the infrastructure will remain operational and under the sole control of the local entity, regardless of any external geopolitical shifts or vendor-level policy changes.
Similarly, IBM is approaching the sovereignty challenge through a software-defined lens, utilizing the Red Hat OpenShift platform as the foundation for what it calls “Sovereign Core” software. This framework is built on the principle that sovereignty must be an inherent architectural property that can be verified through transparent audit trails rather than just a contractual promise. IBM’s strategy allows enterprises to deploy massive, scalable clusters across their own data centers while maintaining a unified management layer that is entirely under their jurisdiction. This architecture supports the seamless deployment of both traditional workloads and intensive AI inference tasks, ensuring that data never leaves the sovereign boundary. By focusing on “provability,” IBM provides the tools for organizations to demonstrate to regulators and stakeholders that their digital operations are truly independent. This transition to software-defined sovereignty allows for the flexibility of cloud-like management while retaining the ironclad security and jurisdictional integrity of traditional on-premises hardware.
Redefining Security Through Sovereign SASE
The evolution of Secure Access Service Edge (SASE) platforms represents another critical frontier in the move toward on-premises digital sovereignty. Traditionally, SASE has been a cloud-native service where security functions like firewalls and web gateways are hosted by a vendor and accessed over the internet. However, vendors like Fortinet and Versa Networks are now pivoting to offer “Sovereign SASE” solutions that can be deployed within an organization’s own private cloud or local infrastructure. Fortinet’s Sovereign SASE offering allows enterprises to manage their own regional encryption keys and identity management protocols locally, ensuring that sensitive access credentials and user traffic patterns never traverse a public cloud boundary. This is particularly vital for government agencies and global corporations that must comply with strict national security regulations while still providing secure, high-performance access for a distributed workforce. By bringing SASE on-premises, these organizations can maintain a consistent security posture without sacrificing control over their most critical traffic flows.
This shift toward “architectural sovereignty” in the security space highlights a broader industry trend where the systems are engineered so that the vendor physically cannot interfere with or access the customer’s data. Versa Networks has echoed this sentiment by offering highly customizable versions of its SASE platform that include configurable geofencing and language localization to meet specific national compliance standards. These sovereign security boundaries ensure that identity management remains under local jurisdiction, preventing foreign entities from gaining insight into the access patterns of key personnel or critical infrastructure. While adopting these on-premises security models requires organizations to take on more operational responsibility—such as manual patching and hardware maintenance—the trade-off is increasingly viewed as necessary. The consensus among security professionals is that the risk of a centralized cloud-based security failure or a jurisdictional overreach far outweighs the administrative burden of managing a private, sovereign security stack that is built to withstand external pressures.
Future Considerations for Sovereign Autonomy
The shift toward on-premises digital sovereignty is ultimately a journey toward long-term resilience and technical self-reliance in an increasingly fragmented global landscape. Organizations that successfully transition to these full-stack sovereign models should prioritize the development of internal expertise, as the responsibility for maintaining “air-gapped” systems and local AI clusters rests entirely on their own technical teams. This involves not only investing in hardware and software but also in specialized training for security personnel who must manage complex updates and audits without the automated assistance of a public cloud provider. Looking ahead, the focus will likely move toward the standardization of sovereign protocols to ensure that different on-premises systems can interoperate securely without compromising their jurisdictional integrity. Organizations must remain vigilant, continuously evaluating their supply chains and software components to ensure that no hidden dependencies reintroduce the very vulnerabilities they sought to eliminate by moving away from the cloud.
As the industry moves forward, the adoption of architectural sovereignty will likely become the baseline for any entity handling sensitive public or corporate data. Future implementations should focus on integrating emerging technologies like confidential computing and hardware-level encryption directly into the on-premises sovereign stack to provide layers of protection that are independent of the operating system or management software. The ultimate goal is to create a digital environment where sovereignty is not a static state but a dynamic capability that can adapt to new threats and regulatory requirements. By taking these actionable steps to secure their infrastructure, data, and decision-making logic today, organizations can ensure they are prepared for a future where digital independence is the most valuable asset. The move to on-premises sovereignty was once seen as a regression to older ways of computing, but it has now emerged as the most sophisticated and forward-thinking strategy for those who recognize that true power in the digital age is defined by what you physically control.