

Matilda Bailey has built a distinguished career at the intersection of networking infrastructure and next-generation wireless solutions, providing her with a unique vantage point on how data flows—and fails—during a crisis. As the regulatory landscape in Europe shifts under the weight of the NIS2

The digital perimeter has effectively evaporated as autonomous AI agents begin to navigate enterprise networks with the speed of light and the authority of a seasoned administrator. The shift from human-prompted AI to autonomous agents marks a turning point where traditional, manually governed

As the landscape of enterprise networking shifts under the weight of artificial intelligence and hybrid cloud architectures, few professionals understand the resulting operational friction as well as Matilda Bailey. A veteran networking specialist with a career dedicated to cellular, wireless, and

The digital backbone supporting global cloud computing is currently undergoing a radical transformation as Amazon Web Services deploys a proprietary routing architecture designed to dismantle decades of networking tradition. For many years, the industry relied on the "fat tree" topology, a
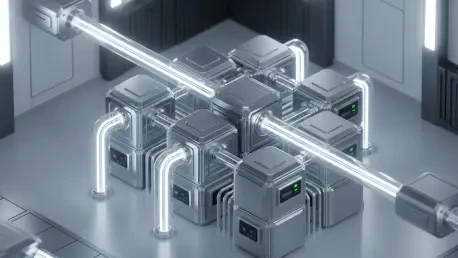
While the pursuit of a singular, massive quantum computer has dominated headlines for years, the true catalyst for the quantum revolution lies in the ability to interconnect disparate processing units through a resilient and scalable networking fabric. At the Cisco Live conference, a transformative

Unexpected hardware failures and incompatible software updates frequently paralyze modern business operations, yet many organizations still wait for a crisis before initiating necessary technological changes. In the current landscape of 2026, the reliance on digital infrastructure has reached a

The global demand for instantaneous artificial intelligence responses has reached a critical tipping point where the physical distance between a user and a central data center acts as a significant bottleneck for innovation. As the industry navigates the current landscape, the reliance on massive

The sheer scale of global data processing has reached a point where traditional silicon and fiber architectures are no longer capable of keeping pace with the exponential growth of hyperscale cloud services. For several decades, the industry has relied on rigid, hierarchical structures to manage

Modern enterprise networks are currently facing an unprecedented surge in data traffic requirements due to the widespread adoption of high-resolution video surveillance and complex Internet of Things deployments. To address these escalating needs, QNAP has introduced the QSW-M2130 series, which

The National Security Agency’s recent introduction of the Zero Trust Implementation Guidelines (ZIG) webpage represents a fundamental departure from the traditional static documentation that has long characterized federal cybersecurity directives. This move replaces thousands of pages of dense,
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65
ITCurated uses cookies to personalize your experience on our website. By continuing to use this site, you agree to our Cookie Policy