

The digital fortress, once thought to be vulnerable only to silent lines of malicious code, is facing a violent transition as explosive-laden drones replace keyboard-wielding hackers. This shift marks a terrifying evolution in global conflict where the physical structures supporting the invisible

Navigating the complex intersection of physical infrastructure and digital assets requires a sophisticated approach to risk management, especially as the data center industry evolves at breakneck speed. Matilda Bailey, a seasoned expert in networking technologies and next-generation solutions,

The sudden migration of top-tier executive talent from traditional technology sectors into the data center industry has fundamentally altered the competitive landscape during the second quarter of 2026. This transition signifies a profound shift in how the digital infrastructure sector views its

The landscape of American telecommunications is currently undergoing a fundamental transformation as the historical obsession with physical infrastructure gives way to a more human-centric philosophy. For decades, the metric of success for national connectivity was measured almost exclusively by

The rapid dissolution of the traditional corporate perimeter has forced a radical rethink of how we secure data in motion, shifting from static hardware to dynamic, cloud-native environments. This transition has historically been painful, characterized by "Franken-platforms" where mismatched
Expert Matilda Bailey is a distinguished networking specialist who has dedicated her career to the evolution of digital infrastructure, with a particular focus on the intersection of cellular, wireless, and next-generation solutions. As data centers transition from isolated private assets into the

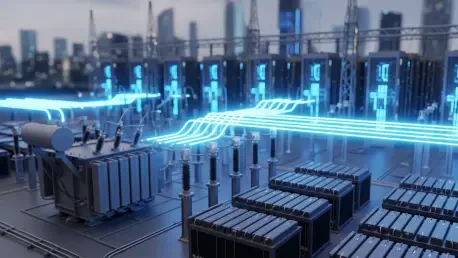
The global race for artificial intelligence supremacy has officially moved from the realm of software code to the brutal reality of physical infrastructure where the availability of power and silicon dictates who leads and who follows. This shift reached its zenith today as Meta finalized a massive

Matilda Bailey is a distinguished networking specialist who has spent her career navigating the intricate intersection of hardware architecture and global security trends. With a focus on next-gen wireless and cellular solutions, she has become a leading voice for organizations looking to fortify
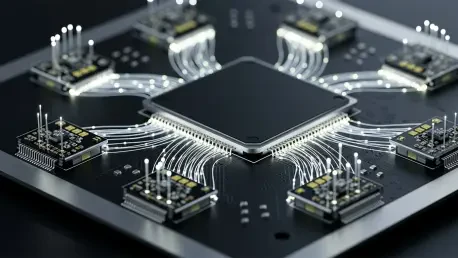
The physical reality of modern computing has finally collided with the uncompromising limits of copper wiring, creating a bottleneck that threatens to stall the progress of artificial intelligence. As Large Language Models and massive neural networks scale toward 1.6T speeds, the electrical traces

The shift toward specialized processing is no longer a niche architectural experiment but a fundamental necessity for any provider hoping to survive the current climate of high energy costs and strict regulatory oversight. As we navigate the complexities of 2026, the demand for localized,
ITCurated uses cookies to personalize your experience on our website. By continuing to use this site, you agree to our Cookie Policy