
The shift from physical server rooms to distributed cloud environments has fundamentally rewritten the rules of engagement for digital defense, turning what was once a perimeter-based discipline into a complex war of identity management. As organizations migrate away from on-premises hardware, they

The digital landscape of 2026 has transformed into a high-stakes arena where the margin for technical error is virtually non-existent for enterprises striving to maintain a competitive edge. Cloud Patrons Info Solutions, an established managed service provider located in Zirakpur, Punjab, recently

The digital fortress, once thought to be vulnerable only to silent lines of malicious code, is facing a violent transition as explosive-laden drones replace keyboard-wielding hackers. This shift marks a terrifying evolution in global conflict where the physical structures supporting the invisible

The digital architecture of the European Union was recently dismantled not by a direct breach of its primary servers, but by a sophisticated exploitation of the very security tools designed to safeguard its cloud infrastructure. This incident involving the Europa.eu platform and the Aqua Security

The rapid dissolution of the traditional corporate perimeter has forced a radical rethink of how we secure data in motion, shifting from static hardware to dynamic, cloud-native environments. This transition has historically been painful, characterized by "Franken-platforms" where mismatched
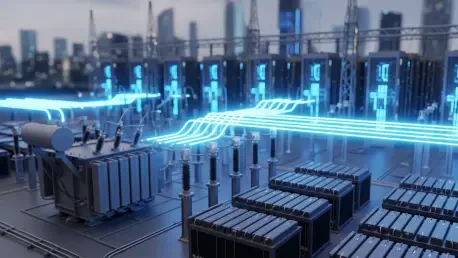
Expert Matilda Bailey is a distinguished networking specialist who has dedicated her career to the evolution of digital infrastructure, with a particular focus on the intersection of cellular, wireless, and next-generation solutions. As data centers transition from isolated private assets into the