
In the contemporary business landscape, where applications, data, and users are distributed across clouds, mobile devices, and global networks, the traditional concept of a secure perimeter has become obsolete. This new, borderless environment demands a security strategy that is not only
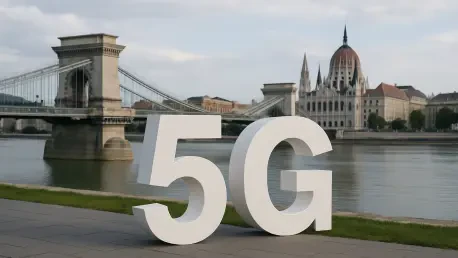
While European consumers may frequently see the 5G icon on their smartphones, a troubling reality lurks behind this symbol of next-generation connectivity, indicating that the continent is critically losing ground in the global technology race. This growing gap extends far beyond simple download

A comprehensive analysis of the American wireless landscape reveals a highly competitive market where the top three carriers are locked in a fierce battle for supremacy, with the latest data showing that while one provider claimed the top overall spot, the margins of victory are often incredibly

The strategic integration of private, on-premises data centers with public cloud platforms has become a powerful engine for business agility and innovation, yet this very integration dissolves the traditional, well-defined security perimeter that organizations have relied upon for decades. This

In the densely populated world of multifamily housing, providing consistent, high-performance wireless connectivity has evolved from a luxury amenity into a fundamental utility, yet delivering on that promise is fraught with architectural and logistical challenges. The complexities of modern

The once-reliable fortress of the corporate network, with its clearly defined perimeter and trusted interior, has become a relic of a bygone era. In today's distributed digital landscape, where data and applications reside in the cloud and users connect from anywhere on any device, the very concept