
Procurement teams keep buying eye-popping accelerators and bigger nodes only to see throughput flatten, jobs stall on shuffles, and energy bills climb while GPUs sit idle because data movement and memory fit—not peak compute—call the shots. The paradox is familiar: systems look fast on paper yet

I’ve spent the last decade living at the seam where deterministic Ethernet meets modern wireless. Across brownfield plants and greenfield labs, my work has focused on turning TSN’s promises into practical reality over 5G. In this conversation, we dig into the craft behind microsecond-level

Introduction In an era where data breaches can cost organizations millions and compromise critical infrastructure, the quest for robust cybersecurity in data centers has never been more urgent, with over 80% of enterprises reporting an increase in cyber threats targeting their systems. This
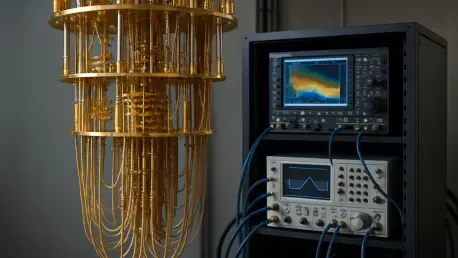
In an era where quantum computing is rapidly reshaping the boundaries of technological innovation, a significant milestone has been achieved that promises to redefine generative modeling. WiMi Hologram Cloud Inc., a global leader in hologram augmented reality technology, has introduced a pioneering

In an alarming revelation that underscores the growing sophistication of cyber threats, a China-aligned threat group known as PlushDaemon has been unmasked as a formidable player in global cyberespionage, showcasing advanced tactics to infiltrate networks. Renowned security researchers have
In an era where cyber espionage continues to evolve with alarming sophistication, a China-aligned threat actor known as PlushDaemon has emerged as a significant player in targeting network devices for stealthy, adversary-in-the-middle attacks. Active since at least 2018, this group has focused its